Hackers have found a sneaky new way to spy on your iPhone — here’s how

One of the many reasons people decide to go with one of the best iPhones over their Android counterparts is due to security. However, as iPhones are known for being less prone to hacking, this also makes them the perfect target for hackers and other cybercriminals.
Now though, it appears that hackers have figured out a clever way to bypass Apple’s security checks through the use of third-party custom keyboards that let them spy on iPhone users.
According to a new report from security researcher Russell Kent-Payne at Certo Software, this new attack method uses malicious keyboards to record private messages, browsing history and even passwords from unsuspecting iPhone users.
Certo decided to look into the matter after the cybersecurity firm received multiple reports of cyberstalking incidents in which the stalkers appeared to know everything that their target had typed into their iPhone. Following its investigation, malicious third-party keyboards were found on all of the affected devices.
Whether you use an iPhone with a third-party keyboard yourself or are worried about being spied on, here’s everything you need to know about this new threat including steps you can take to protect yourself.
Abusing TestFlight to install custom keyboards
Normally when it comes to spying on iPhone users, an attacker would need to jailbreak a target’s device or gain access to their iCloud account. What sets this new attack apart though, is that it doesn’t rely on either of these methods to spy on iPhone users.
Although they’re not normally dangerous, this attack weaponized third-party keyboards by using malicious ones to serve as keyloggers on vulnerable devices. From here, a hacker can discreetly capture and transmit all of the keystrokes an iPhone user makes on their device.
While Certo didn’t go into all of the nitty gritty details about this attack to avoid providing other hackers with a blueprint, it did explain how it works. To reach potential victims, the hackers behind this campaign are abusing Apple’s own TestFlight platform which is used for testing new iOS apps before they’re released on the App Store.
By putting out their malicious keyboards via TestFlight, the hackers are able to avoid being detected by Apple since apps on the platform don’t undergo the same rigorous security tests that App Store apps do. However, as Kent-Payne points out in his report on the matter, a malicious custom keyboard could theoretically be distributed via any app.
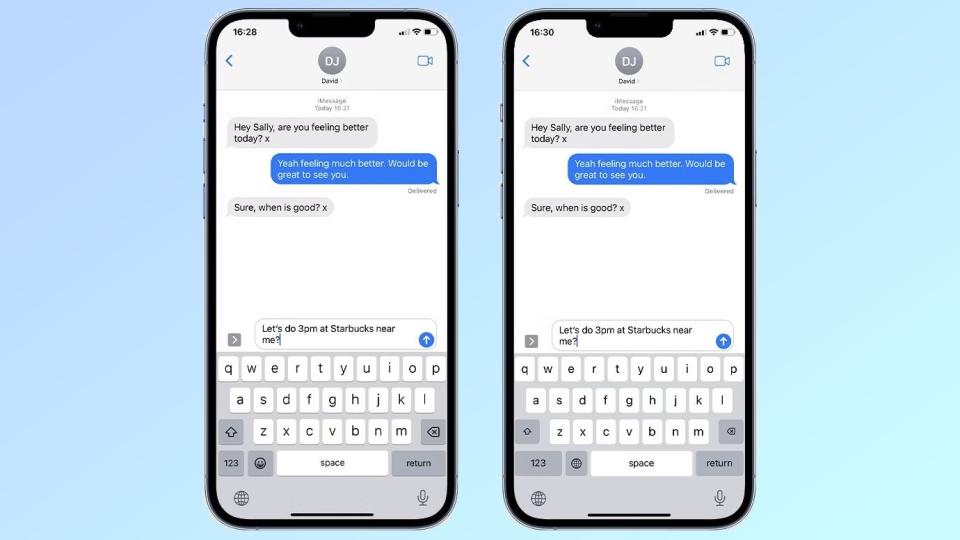
Once the TestFlight app is installed on the targeted iPhone, the hackers install a custom keyboard via the Settings app and configure it so that it has “Full Access” to the device. From here, they then switch the iPhone’s default keyboard with this custom version which is visually indistinguishable from Apple’s stock keyboard.
The malicious keyboard is then able to record everything a victim types and all of this information is sent back to a command and control (C&C) server operated by the hackers behind this campaign.
How to see if hackers have installed a malicious keyboard on your iPhone

If you’re worried that there might be a malicious keyboard that’s working as a keylogger installed on your iPhone, Certo has provided a few steps to see if you’re affected.
To get started, open your iPhone’s Settings app and then go to General, Keyboard and finally Keyboards. Here, you’ll see two standard keyboards: One in your language and another named “Emoji”. If you see another keyboard here — like one you don’t remember installing — this could be cause for concern, especially if it has “Allow Full Access” turned on.
If this is the case, you’re going to want to remove any unrecognized custom keyboards. This can be done by tapping on Edit, tapping the red minus button next to any keyboard you don’t recognize and then tapping Delete.
For those looking for extra protection for their Apple devices, you should also consider installing the best Mac antivirus software. While there isn’t an iPhone equivalent of the best Android antivirus apps, both Intego Mac Internet Security X9 and Intego Mac Premium Bundle X9 can scan your iPhone or even your iPad for malware but they need to be connected to your Mac via a USB cable.
At the moment, Apple hasn’t said anything publicly about this new attack method but we’ll update this piece if and when the company does.
